Having studied unsolved cipher mysteries for more than a decade, it seems to me that there are some distinct patterns of behaviour around them (by owners and by others) that serve to muddy the waters for modern researchers.
And so for the sake of collaborative clarity, I think that each of these behaviours ought to be given a ‘pattern name’. (There’s a very large “Patterns” literature in Architecture, Computer Science and Management, where common patterns of behaviour [both good and bad] are given names.) You may agree or disagree with the specific examples I give (and/or you may have a better pattern name in mind), but please hear me out, see what I’m trying to get at here…
“Cipher myth-making”
This behaviour typically occurs in the situation where someone has inherited or found an unsolved historical cipher, but has no provenance or definite historical context to work with. Unable to solve the cipher, the owner then (for whatever reason) concocts a myth or legend around it that they would like to be true.
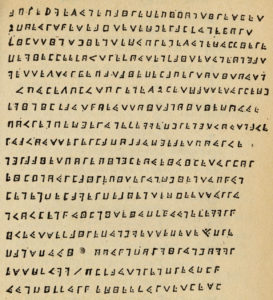
The prime example here would seem to be the first version of “La Buse”‘s cryptogram (as famously described by Charles de la Roncière in his 1934 book “Le Flibustier Mysterieux”).
To my eyes, the odds are high that this was found in a notarial archive but with nothing accompanying it to help place or date it. And then, perhaps inspired by the early twentieth century Mauritian “gold rush” to find the Nageon de l’Estang pirate treasure, the owner presumed (though without proof) that it was a pirate treasure map.
My guess is that the myth that was added here was that of Olivier Levasseur hurling a treasure map into the crowd just before his execution, and exclaiming “Mon trésor à qui saura le prendre“. (There is, as far as I can tell, not a jot of evidence to support the idea that this melodramatic little scene actually happened.)
Without that, why would anyone link the cryptogram with La Buse?
“Cipher backfilling”
This behaviour occurs when the unsolved cipher has some kind of story already associated with it, but the absence of useful support details offers an evidential vacuum that demands to be filled in.
This differs from cipher myth-making in that here some kind of basic story needs to first be in place (though whether that story itself is true or false is another matter entirely): the additions are then in the form of elaborations to the core narrative, fleshing out its skeletal structure.
The obvious example of this would seem to be the second “La Buse” cryptogram:
Here, the elaborations would be the extra lines of cipher (some apparently cribbed from Poe), the drawings (some apparently cribbed from Howard Pyle), and the pigpen ciphertext saying “LA BUSE” (apparently cribbed from the myth).
The Beale Papers?
As with the two different “La Buse” cryptograms, the evidential haze around many other unsolved cipher mysteries can exhibit both cipher myth-making and cipher backfilling at the same time.
For example, I think there’s a strong argument that while the Beale Ciphers themselves could well be genuine, the case for the Beale Papers‘ being genuine is somewhat less straightforward.
The supposed bedrock of the history is that Beale placed an iron box with the cryptograms in trust with an innkeeper called Robert Morriss, who then opened it 23 years later (in 1845). However, the well-known problem with this timeline is that Morriss did not start work at the Washington Hotel until 1823, which was apparently after the box had already been left.
This suggests that Morriss may well have inherited the box from a previous innkeeper at the Washington Hotel: and that even if Morriss knew the correct name of the box’s owner (which was presumably, but not necessarily, written on the box itself), he may well never have actually met him.
This further suggests that Morriss may have taken the basic story about how Thomas Beale left a box at the Washington Hotel in the early 1820s and backfilled it until it became a tale worth telling and re-telling (while perhaps also advancing his personal claim on any treasure that may get found on it).
Moreover, it would seem that Morriss’s tale was then further elaborated by the (unnamed) author of the Beale Papers, until it became a tale worth printing (and hopefully buying).
However, if you put the Beale cryptograms to one side, I don’t currently see any evidence that anything about the Beale Papers is genuine, not even Thomas Beale’s name. Which perhaps goes to show how careful you have to be when trying to make sense of cipher mysteries.
The Voynich Manuscript?
It could well be that the the 1665 Marci letter that famously accompanied the Voynich Manuscript contains distant echoes of previous cipher myth-making: its suggested link to Roger Bacon now seems somewhat spurious, but was notable enough for Raphael Mnišovský to remember some decades later.
The supposed link between the Voynich Manuscript and John Dee / Edward Kelley is somewhat easier to deal with: without any real doubt, this was Wilfrid Voynich’s own cipher backfill. But his notion that the only conceivable way the manuscript could have travelled from England to Bohemia was via Dee and/or Kelley seems both historically and intellectually unsatisfactory.
Perhaps the bigger story here, as I’ve argued elsewhere, is that the Rosicrucian Manifestoes might possibly be the most extraordinary cipher backfill ever, i.e. that they were part of a huge after-the-event false history construction designed to appropriate the Voynich Manuscript into a scheme to con(vince) Holy Roman Emperor Rudolf II into backing a proto-Freemasonic group. But we may never be able to determine whether or not this is true.
Nowadays, there seems to be no end of people putting out YouTube videos and websites with Voynich-related backfill: indeed, perhaps the biggest challenge we face going forward is swimming through the brown tide of cipher backfill. Oh well!

Cathars, @nic, where can I query it?
Pete: you might start with a 2013 post here:
http://ciphermysteries.com/2013/07/27/voynich-manuscript-an-andean-sky-god-cathar-theory
Thanks, looks like it might be worth another shot, if only to us in the trenches.
Pete: if it is a shot, it’s only in someone’s foot. Try to make sure it’s not your foot.
It’s all in the balance, your negatives against all positives. Then we can judge.
Pete: judge all you like, but only meddling in the evidence room by the Hand of God could make a truly terrible Cathar Voynich theory workable.
And so far, all Cathar Voynich theories I’ve seen are truly terrible.
Wot if the innkeeper got the name muddled up and it was really Thomas Keane….
/tic
NB I assume when you talk about the Beale Ciphers plausibly being “genuine” I assume you mean in so far as they might actually encrypt something, rather than the contents of the plaintext actually being anything other than a wild imagination or a good story….?
Milongal: there seems to be good reason (as far as I can see, at least) to think that the Beale cryptograms B1 and B3 are genuinely enciphered, and indeed enciphered using the DoI in some way.
As to the rest of the Beale papers… it’s really not so clear that they will prove to be a help in any useful sense of the word. :-/
Hi everyone,
It looks like clearly a fake…
1- too many drawings! You ciphered instructions to find a treasure in a certain way. So why the hell using all these drawings??? If it was from La buse:
× he is very good at drawings and he drew his sentence to death by hanging. What a visionary!!
x quite a big stuff to be hidden in a necklace!
2- the 5 last lines are the clearest compared with the 17 first lines! It really looks like as the scarabée d or de Edgar Allan Poe
3- the last line is his date of death so he wrote his crypto close to his end!
4- some drawings look like some in the very good internet site officiel Yannick Benaben!
A few days ago, i watched in YouTube an interview of Emmanuel Mezino.
He said that the 22 line cryptogram was dated of the fifties but it was surely a copy of an older cryptogram which would have belonged to the same family (heir of Nageon de l Estang. Savy?)
My theories of the subject:
×The 17 line crytogram of le Flibustier mysterieux is not a copy of Charles de La Roncière. It is a photography made ine the Bibliothèque Nationale where he worked. It is written in the original book. You can go to the site pirate and corsaires and look up Olivier Levasseur biography and find the cryptogram with a very resolution.
x the 22 line cryptogram is false. I think it was made by Savy’s family (or why not de la Roncière???). The person who copy it was not a specialist beacause the 17 line cryptogram is more complete. So, probably not de la Roncière ! It is like à try to decipher the mystery with those drawings. The Savy family had this one that is why they could have sell the original one to the Cruise Wilkins.
x people who use this 22 line crypto do not understand the 17 line crypto that is why they fully think that it is the original…
x Nageon de L Estang never found this treasure! Indeed, he let this cryptogram
ith the other letters on his testament
x I do not share the conclusions of de La Roncière where he mixed the crypto with other coded indications (Butin’s ones).
You can also go to my blog. I give small indications which are hidden in my dialogues with the Buzzard. I also give the exact “location” of the treasure of the page cagnotte leetchi. I never saw the same theories on other website. The use of google translator is highly recommended for non french speaking.
@Nick: do you believe in this cryptogram ?
From Olivier Levasseur? Maybe, maybe not? But, Nageon let in his testament some “treasure” maps so….???!!!
@Nick: have you ever had a look on my blog? I know it seems like speculations but i do not want to reveal the way of deciphering the 17 line cryptogram.
Regards
Hi,
Here is my blog:
“Https://cryptogramme-olivier-levasseur-labuse.blogspot.com/”
Feel free to send me a message or comment on this blog
For two years, i have read lots of books regarding the pirate Olivier Levasseur and his supposed cryptogram.
The recent interview of Emmanuel Mezino on youtube in which he gave some revelations made me want to read again some chapters of of his book “mon trésor à qui saura le prendre ”
I still do no understand the whole logic and the link with the inscriptions in the cave.
His logic:
-1the 2nd cryptogram is the original more complete (drawings, more letters on the 15th line
2- With the second cryptogram, many hidden signs in the drawings would give indications with the stars
3- triangle made by linking what look like a A in our alphabet (his letter Y using the key of masonic alphabet. Other site a z)
4- inside this triangle, you can find the word Ecu so the linking with Ecu de Sobieski
5- after i did not understand the logic. Sorry Emmanuel 🙁
Bye
Waiting for your comments
Hi
For two years, i have read lots of books regarding the pirate Olivier Levasseur and his supposed cryptogram.
The recent interview of Emmanuel Mezino on youtube in which he gave some revelations made me want to read again some chapters of of his book “mon trésor à qui saura le prendre ”
I still do no understand the whole logic and the link with the inscriptions in the cave.
His logic:
-1the 2nd cryptogram is the original more complete (drawings, more letters on the 15th line
2- With the second cryptogram, many hidden signs in the drawings would give indications with the stars
3- triangle made by linking what look like a A in our alphabet (his letter Y using the key of masonic alphabet. Other site a z)
4- inside this triangle, you can find the word Ecu so the linking with Ecu de Sobieski
5- after i did not understand the logic. Sorry Emmanuel 🙁
Bye
Waiting for your comments
@Nick
Hi, are you reading “Mon trésor à qui saura le prendre” for the third times ?
Unfortunately, you never answered 😥
Regarding this legend, you were more talkative or active a few years ago…
All the best