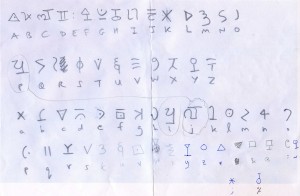
As promised, here are my work-in-progress transcriptions for the newly-released pages #7 and #8 of the Blitz Ciphers. I’ve had to add a few new symbols to the transcription alphabet, so there are now about sixty or so: doubtless some will prove to be duplicates, but I’d rather slightly expand the alphabet when transcribing than make a wrong assumption that can’t easily be undone.
And what do they tell us? Well, I’ve already tried a series of statistical tests on them, though without anything jumping out so far. Even though they have a trailing-off instance count distribution with E at the top of the heap and D not far behind it, the rest seems fairly arbitrary.
Unlike Dave Oranchak, I haven’t spent years thinking about how to crack unbroken homophonic ciphers, so I don’t really know if this is expected behaviour. Some of the symbols could well be nulls, but I don’t (yet) have a good tool for predicting homophonic nulls: but maybe that’s just too old-fashioned a thing to hope for.
Here are some analysis links to Dave Oranchak’s Webtoy: page #7 analysis and page #8 analysis. Note that these only worked for me in Firefox (not IE), but other browsers may also work.
Overall: as of right now, I’d say the Blitz Ciphers looks a bit loose and patternless: in particular, the contact tables don’t quite ‘feel’ right.
Yet unlike Rich SantaColoma commenting on Klaus Schmeh’s page from a few days ago, I’m not yet ready to call this as an outright fake. Rather, what I’m saying is that the Blitz Ciphers seem to combine the instance frequency counts of monoalphabetic ciphers with the disorder of polyalphabetic ciphers and the inscrutability of homophonic ciphers. Two out of the three I could probably still feel comfortable with simultaneously (and work with), but having all three in play at the same time leaves me a bit… suspicious.
Basically, the jury’s out on this one, and they’re asking for pizza.
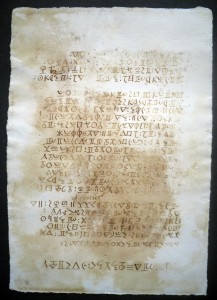
Page #7 (rotated 180 degrees from the image as released):
CAV~MrMmEewmDFT
BedaDeBCMmazMCTfr*TRE
rBe.qREmdp*&Y&bzMDEw;
jes.q&pCM.Ydfejqz
IgRD.JWqEED.aECMqul
*YdqeMBC.epRBmLTT
CeMEDBjEYAeNFLQXXqf%REqA
DkC.eEBRAYrlTjJEYWFvI
Mf.XaKQjeCy*zjMLQd
D.eDEQjlJa.IMdT
Tgj.DdQl.GzHu.wAdzY
Dp.z*kECEzEkCwmedYT
CMETCzDkCzrYDE&RgdVX
CMExLRpde&TrYjDEweedDC
CTMEDkEk&wMjqEArVSSdK
DCTkEISABeDdylbIdRMEDY
gQl@AeqEM*jRSMYwrdeDl
*eeqElYeSME*uVKk.elKLm.
eEDELCYLNTgRm:Jd..zaDtdM
VVDdgEDIRCgjm..erzd
DEDedgLCvkEMjD.z*kEjMLglE
REdf*EDRJBBDba.KIZEZpH
Cj.fDnzjE.aET.lE
jeeSq.zAE
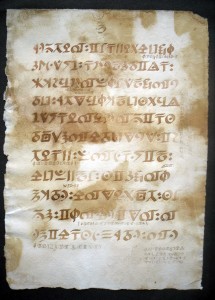
Page #8
nedXYjEDbzqYaFIUS
tLpTQkEZBWJMHDAZE
KgRiBjGSbTJUCW
HIEnXciSgJIlaiA
kTQZYjYBjdDZl
HfsMCFHIcWTEDR
XYZqEGCpZ.QDJE
FIGqJbElDtUjS
MgHeEFjCHafXElb
dMEDSjFIDcjEj
eMDFZlpVnHeECe
Note that my expanded transcription alphabet looks like this (click for larger image):-
Nick, have you had an opportunity to compare the mystery script with Ottoman/Turkish/Cyrillic/Anatolian/Czech/Bosporus handwritten scripts? Basically domed structures such as the Hagia Sofia?
I’m trying to remember the details of the elaborate mansion, turkish bath, hot water system which hot wastewater was run off into the glass greenhouse. You may be able to get more details from the person who has been passing the puzzle pages to you.
If I were ever able to visit London, I would probably be making a bee-line to the North Campus and Library of Greenwich University. Somewhere there has to be archives and discussion of the development of the North Campus, at least.
bdid1dr
What if, in addition to rotating, you were able to flip the page front to back (or back to front) or mirror image?
I’m trying to remember the more modern techniques of preliminary drawings/drafts that were required before preparing a blueprints and transparencies.
?
beady eyed (squintier) wonderer
It is rotated, not mirrored. There are a number of clues:
* The glyphs are rotations of the glyphs on other pages
* Non-justified text reads from the side that’s flush with the edge of the page to the side that’s staggered, and paragraphs tend to end with a shorter line.
* The general flow of the page: The single larger typed header should be at the top.
@PortP: I am not talking mirror image, but rather reversing the margins by simply turning the page as if it were bound in a book. If this explanation isn’t quite clear in meaning, may I ask you to put your hand in front of your face (as if it were a piece of paper writing on it) then flip it over (from right to left, as if to see if there is any writing on the back side…….
This works best with semi-transparent paper.
Rather than using a mirror, which can get rather tiresome, one can move along at a smoother and faster rate of transcribing.
I bet Nick has even more sophisticated (electronic) means of doing what I just outlined. Eh, Nick?
big smile: elims gib
🙂
Not that I’m smiling glibly; just trying to illustrate my observation that if one is able to determine the colors of the tiles, and the geometric forms being made, the script would probably make sense. The tiny postcard which I found on the WWW seemed to portray ‘saraband’ layout. The overall pattern seemed to be skulls. I don’t think we had the convenience of color photography yet in the early 1900’s.
?
Yesterday I did a little research into the source of Avery North’s wealth. It appears that he was one of many ‘entrepreneurs’ who exported guano (nitrate fertilizer) from islands offshore from Chile.
Charles C. Mann has written several books, in collaboration with David H. Freedman, Mark L. Plummer, and Robert P Crease.
Titles, of which I will be requesting at my public library:
1491: New Revelations of the Americas Before Columbus
1493: Uncovering the New World Columbus Created
Noah’s Choice: The Future of Endangered Species (with Mark Plummer)
“The Aspirin Wars: Money, Medicine, and a Hundred Years of Rampant Competition (with Mark Plummer)
“The Second Creation: Makers of the Revolution in Modern Physics (with Robert Crease)
So, I’m still trying to stay within the bounds of the Blitz Cipher discussions by referring you to the source of Avery North’s wealth: seagull dung — a whole island/mountains of it.
So, is it no 1-dr that Avery North required a Turkish-style bath-house — and maybe lots of fertilizer for his green-house/orangerie?
bdid-1-dr-r
😉
The “Blitz” cipher. For those of you who might be 1-dering why is this discussion called the “Blitz” cipher; and why is it called a cipher. The pages Nick is referring us to are remnants of plans and spec’s for Avery North’s mansion’s Turkish steam bath and attached greenhouse. After North’s death, the property deteriorated somewhat, but eventually became a schoolhouse/academy for women to be taught how to be teachers. It apparently was active right through the 1930’s and until the outbreak of World War II. The Blitz did considerable damage to London and outlying areas — including the old Teacher’s College.
Sometime last year, Nick introduced us to the plans and drawings which were being given to him by “anonymous”. I am firmly certain that the items now being discussed are the plans and spec’s for that old College which apparently was badly “Blitzed”. I’m hoping that Nick will be conferring with “anonymous” — who may also be able discuss where and how these documents ‘came to light’. I vaguely remember mention of a nephew bringing forth the material?
Still 🙂 ing!
beady-eyed wonder
Nick & Friends, I once again took a bird’s eye view of the Avery Hill Campus of Greenwich University. So, maybe it wasn’t a Turkish Bath building; but the overhead view of the Mansion site clearly shows the domed roof (glass?) of Avery North’s huge mansion. The University has posted a beautiful one-page labelling of the Mansion Site and the Southwood Site.
I think you will now be able to read the pages of the “Blitz-Cipher” plans and specs (which are quite water-specked)?
I’m hoping you might take a walk through the Mansion Site (which Library-ian may be able to take you on a tour of the domed section).
Who knows, perhaps a student of the School of Architecture (in the same Mansion campus) might be able to translate the Blitz ciphers for you. ? 😉
My earlier reference to the “North Campus” is incorrect; the correct reference is the “Avery Hill” Campus.
The full name of the owner/developer of that mansion and its ‘winter garden’ was ‘Colonel’ Avery North. Some historians refer to him as identifying himself as ‘Colonel’.
At this point, having done a whole lot of web-surfing, I can’t recall where I got the first name for Colonel North as being Avery. Anyway the person who commissioned the huge mansion and it’s attached “Winter Garden” with its enormous, beautiful, glass dome, apparently was named John/Jonathan (?) North.
Nevertheless, the “Blitz Cipher” is ALL about the architectural notes, diagrams, and methods of turning an octagonal based glass structure into a round dome. For the times, I suspect the glass panes were inserted into cast-iron framework.
Some recent reading tells me he fired the architect midway in the building process. One comment from a recent visitor mentions her experience with the School for Teachers, and the Blitz.
😉
(Hopefully this will be the last weekend I have to type on a laptop. Hopefully a new computer is in process of being built for me — the guys promised 3 or 4 days delivery.
The “Blitz Cipher” is all about diagramming and drafting preliminary drawings, calculations (triangulating) and plans for building an octagonal-based glass-pane dome. The beautiful finished product is still in use as a Winter Garden for tropical trees, bushes, and cacti . Some of the visitors to Greenwich University’s Winter Garden have left comments about their experience as students, teachers, and staff when the Library and School (domed) were intact previous to the Blitz.
Today, the Avery Hill Campus of Greenwich University holds regular visitors days and other community events. They have a very good comments page.
🙂
Apparently Cutler (designer/architect/builder of the domed “Winter Garden”) was fired by J. T. North. From further reading, these past two days, I’ve discovered that J. T. North was Jonathan Thomas North — who DID make his fortune by importing South American guano for use of very wealthy European (English) gardeners.
😉 smiley with a squint
Book: The Nitrate King – A Biography of “Colonel” John Thomas North. Book written by William Edmundson, publisher palgrave macmillan.
Fascinating!
🙂