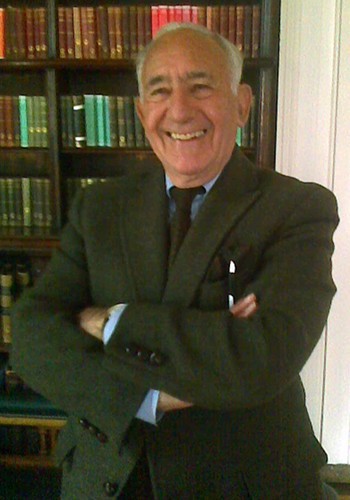
A few days ago, I grabbed the chance to meet up with renowned crypto writer David Kahn at the Athenaeum Club in London while he was attending a conference on the Battle of the Atlantic. It was… simply a pleasure.
He very happily signed my well-thumbed copy of “The Codebreakers” (1967), though I have to say it barely seems possible that he wrote his crypto meisterwerk close to half a century ago. He continues to research and write on crypto topics: a collection of his articles (“How I Discovered World War II’s Greatest Spy and Other Stories of Intelligence and Codes“) is due to be released in October 2013.
All that aside, he was eager to know about what was happening in the world of Voynich Manuscript research (and delighted to see my rather battered copy of Gawsewitch’s “Le Code Voynich”, even if it isn’t actually a facsimile edition) and urged me to write a state-of-the-art-circa-2013 summary of it for Cryptologia (he was one of its founders). Incidentally, he half-remembered being told recently that someone had cracked the Dorabella Cipher (which is possible, though slightly unlikely, I’d say).
But alas, my all-too-brief hour was up too soon: I had to leave and once more merge into the grey London streets. Yet the whole thing set me wondering for several days how best to summarize the Voynich Manuscript. Why is it that Voynich researchers can know so much about the manuscript’s minutiae, and yet agree on almost nothing? Why is it that the Voynich’s Wikipedia article is so long, yet says so little? Why write another analysis-paralysis piece on it?
Part of the challenge is that it often feels to me as if nobody has written a single word on the Voynich Manuscript that even remotely does it justice. Rather, it’s as if there’s a honey-pot of non-words and non-phrases for non-historians to dip their paws into, making every article and blog post written on it little more than a sweet (though ultimately unsatisfying) anagram of the preceding ones.
At the same time, in my own Voynich research it’s as if every day is Groundhog Day, where pretty much everyone else in Punxsutawney never learns anything, but instead sticks belligerently to their same futile and unhelpful non-positions, day in and day out. [*] For example, I would agree that it is entirely possible to construct alt.histories where the Voynich post-dates the 15th century (oh yes, and that the palaeography, the codicology, the Art History and the radiocarbon dating are all simultaneously wrong, or perhaps hoaxed in a peculiarly sophisticated way), but why on earth would anyone bother?
It’s a lot like fighting against a kind of post-modernist debating society, for whom the inevitable existence of doubt in any given fact makes it fair game to dismiss it. Such en masse debating may well be a great way of passing time, but it’s surely a lousy way of getting to the truth. I’m not interested in knowing what might conceivably have happened, I want to know what genuinely did happen.
*) All the same, I’m getting pretty good at ice carving. That’s bound to come in useful one day… 🙂