I’ve spent twenty-odd years thinking about the mystery of the Voynich Manuscript’s gallows glyphs; and I thought I’d post about how I believe these glyphs evolved. Whether or not I’m right probably doesn’t matter much, because I suspect I may be the only researcher looking at this particular mystery.
The only similar attempt I can recall was when Steve Ekwall posted about the “folding key” (that had been revealed to him by an Excitant Spirit), plus his other page here. What I’m doing here isn’t remotely like that, but seeing as nobody has mentioned Steve in a decade or more, I thought his pages could do with a bit of link love.
My Core Beliefs (About Voynichese)
Cryptographically, my core beliefs about how Voynichese happened are:
- Voynichese did not appear ex nihilo (it’s far too sophisticated and tricky)
- Rather, it was an evolution and a merging of earlier fifteenth century cipher systems / tricks
- If we look carefully, we can catch glimpses of those earlier cipher systems / tricks
- Its structured glyph patterns point away from mid-fifteenth century homophonic ciphers
- Instead, its small cipher alphabet points to other tricks, e.g. steganography and transposition ciphers
- As far as arbitrarily complicated transposition ciphers go, there is a single reference (in Alberti), but we have no matching transposition ciphertexts or other contemporary references to rely on
As far as what the other component cipher systems might be, my inference has long been that one of them was originally a verbose (paired glyph) cipher designed to steganographically conceal the visual presence of Roman numbers. For example, if CLXVI were each encoded as or [C], ol [L] / am [X] / al [V] / ar [I], the number LXXXVII would encode as olamamamalar. Note: this may not be quite how it ended up being used in the Voynich Manuscript, but my guess is that this is where these verbose pairs came from.
What, then, of the gallows glyphs? Where did they come from, and what happened to them along the way? These are the kinds of questions this post is trying to answer (however imperfectly).
Oh, and before I launch into the different evolutionary stages, my core belief is that the gallows glyphs have retained their original shapes throughout all this, but that their function has expanded and developed. Just so you know.
Evolution #1 – Cipher Alphabet Selector (x2)
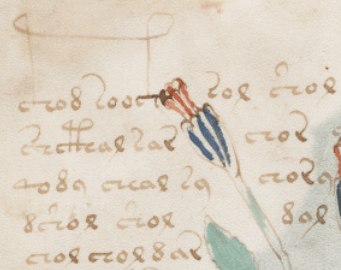
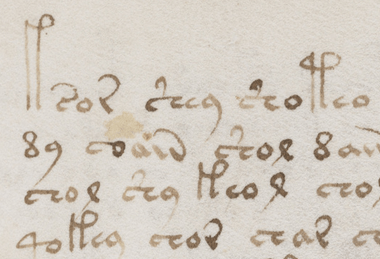
In the first evolution, I believe there were exactly two gallows glyphs, and that they had the same shapes as the Voynich Manuscript’s EVA t and EVA k. These would have been used only in the first character of a paragraph of ciphertext to indicate one of two cipher alphabets to use, visually concealed as a scribal flourish. We still see echoes of this earliest evolution in Herbal A pages (but mainly p-glyphs), such as the page-initial glyphs on f8v (EVA t) and f27r (EVA k):
The specific reason I think this is because of their shapes: I believe the shapes of these glyphs signalled to the decipherer not only which of two cipher alphabets to use, but where on the cipher ledger page to look for that cipher alphabet. That is, the cipher ledger page for the overall cipher would have contained two ciphers, one written out horizontally (EVA t) and one written out vertically (EVA k).
In a way, this would have been like an early homophonic cipher, but crossed with steganography. It feels like a branch of cryptography that had not yet hit its mid-fifteenth century stride, but as an evolving practice of secret writing whose history had yet to be written. Hence I’d tentatively date this first layer to the 1420s or maybe the 1430s.
Have I or anyone else seen a page of a cipher ledger with both a horizontal cipher key and a vertical cipher key? No, I don’t believe so: but nonetheless I still believe this was the first stage of the glyph evolution.
Evolution #2 – Fake Cipher Alphabet Selector
The next evolution introduced fake cipher selector glyphs at the start of paragraphs and pages – EVA p and EVA f. I believe that this usage is a feint, designed to make code-breakers suspect (wrongly) that the ciphertext they’re trying to crack uses the older cipher system: and that this is exactly what we see in the Voynich Manuscript.
But… why introduce fake cipher selector glyphs at all? My belief is that the cipher creator introduced the (stage 2) fake gallows glyphs to replace the (stage 1) original gallows glyphs, because they wanted to reuse the original glyphs for a different (but related) cryptographic trick, which we’ll see in the next section.
Also: I believe this second stage implies that the cipher creator had shown the first evolutionary stage to multiple potential patrons, in an attempt to sell his cryptographic / intelligencer services to them: or else there would have been no need for tricky misdirection. So I believe this tells a story not of a complete outsider, but rather of someone on the periphery of one or more fifteenth century courts, trying to use their cryptographic smarts to gain patronage.
Evolution #3 – EVA k = Vertical Transposition Cipher Token
In this third evolution, EVA t still referred to a horizontal cipher key and EVA k still referred to a vertical cipher key. That is, the glyph shapes retained the original visual cue to where on the page to look for the key, but the keys had moved to a new place (and on a new page).
So, where are these putative keys? I’ll start with the vertical key: it’s the first token (which might be a glyph or a glyph group) inserted at the start of each line. The idea that there is some kind of insertion going on at the start of lines is an idea that has been floated for decades, e.g. supported by statistical studies indicating that the first word of a line is normally a little longer than the second word. This of course plays havoc with vocabulary (because it yields lots of unique words) and any proposed explanatory grammar (because line-initial words mess up nice neat models).
All the same, few have proposed explanations as to what this vertical key might be for. Philip Neal in particular talked about this a lot: in his honour, these letters are often described as a “vertical Neal key”, though I believe he never felt comfortable hypothesizing about what that might mean cryptographically.
Me, I’m far more comfortable with hypotheticals, because otherwise we keep on hitting Wittgensteinian “whereof walls”. Here, my hypothesis is that EVA k is a transposition token that decipherers should replace with the token inserted at the start of the line. This makes this mechanism it very much a transposition cipher, but rather than a rail-fence cipher (which kind of relies on seeing letters as movable type, and is therefore more of a post-Gutenberg transposition cipher) it is a line-centric transposition cipher.
For an encipherer, then, the sequence would be something like this:
- Scan though the whole of a single plaintext line
- Find the (I imagine) single consonant that appears the most on that line
- Insert an enciphered version of that letter at the start of that line
- All instances of that letter within the line would then be replaced by EVA k
Let’s try this on a concrete example:
TO SLEEP PERCHANCE TO DREAM AY THERES THE RUB
FOR IN THAT SLEEP OF DEATH WHAT DREAMS MAY COME
OK: the most common consonant in the first line is R or T (four times each), and in the second line T (four times). So, replacing the first line Rs and the second line Ts with $ (standing in for EVA k) gives:
RTO SLEEP PE$CHANCE TO D$EAM AY THE$ES THE $UB
TFOR IN $HA$ SLEEP OF DEA$H WHA$ DREAMS MAY COME
Now, on its own, this cipher trick is far from fearsome: but when arrayed as one of a carefully chosen set of cipher tricks, I think it can be quite the monster.
Evolution #4 – EVA t = Horizontal Transposition Cipher Token
Whereas the third stage was a line-centric transposition cipher (i.e. you didn’t need to look beyond the current line to encipher or decipher the text), this fourth evolution is a paragraph-centric transposition cipher. What that means is that a horizontal key is concealed somewhere in the paragraph, and that each time a decipherer encounters an EVA t in the text, they replace the EVA t with the next token along from the horizontal key.
OK, so where is this horizontal key? There seems little doubt to me that it will always be found somewhere on the top line of a paragraph. My suspicion is that in the earliest iterations of the cipher, this horizontal key may well have been placed right at the start of the paragraph. But as time went by, this was seen as a weakness, and so the encipherer would have needed to (what code-makers call) “bury” it inside. (For example, Typex used “buried codresses”, though this always sounds to me like an elaborate fish funeral.)
So, where on the top line of a paragraph should we be looking for these horizontal keys? In my previous post, I went looking for model-unfriendly long words: two of these (highlighted by Mauro) were in Q20 on the top line of paragraphs – chkaidararal on f115v, and shoefcheeykechy on f104v. These could very easily be horizontal keys, right? While that’s indicative, that’s really not systematic enough.
Once again, Philip Neal possibly comes to our rescue. One Voynichese behaviour he has long been intrigued by is the presence of pairs of words on the top line on paragraphs where both words contain EVA p. Philip wondered whether these pairs might somehow be signalling or bracketing a key phrase of some sort: though, as before, he remained hesitant about lurching forward from there into some kind of cryptographic hypothesis. But all the same, it has to be said that these p-paired horizontal Neal keys feel a lot like some kind of metatextual feature, whether a concealed title, or colour hint or what.
Whatever the actual explanation for these Neal keys, they feel almost consciously designed to disrupt nice neat statistics and/or linear language hypotheses about Voynichese. For if you take out all the paragraph-initial EVA p instances, as well as all the EVA p instances in p-paired horizontal Neal keys, then the number of EVA p instances remaining in the text drops down to almost none.
So… where exactly on the top line of a paragraph are the keys? What is the tell for a cipher key? I… don’t know. Yet. But I continue to look. Today I’m wondering whether I might be able to work backwards from odd words like chkaidararal and shoefcheeykechy to understand the visual cues on the page placed there to help a decipherer see the key. And the final answer may well have something to do with horizontal Neal keys. Hopefully we’ll get there before too long.
Evolution #5 – Where Transposition Doesn’t Work
A key problem with these two transposition ciphers is that they rely on you having neat lines and neat paragraphs to embed keys in. But what about pages built around circular diagrams? Here there is neither an obvious top line, nor an obvious line-start to insert before. So I believe a different kind of key would be needed.
For what it’s worth, I believe that an additional verbose cipher was introduced for these pages: ok / yk / ot / yt. Just to make things difficult for you. So I therefore think that “ok” is a verbose cipher, but “k” is a transposition cipher. But I might be wrong.
OK, So Where Next With All This, Nick?
I first suggested much of the above in “The Curse of the Voynich”, nearly twenty years ago: so for a fair few Voynich researchers this is far from breaking news. All the same, there’s lots of other stuff here that is new, so I think it was worth bringing the thread a bit more up to date.
Really, the big ‘where next‘ step here is simply to see if there’s some kind of visual cue (or an evolving set of visual cues) that signals to the decipherer exactly where a horizontal key is buried (e.g. on the top line of a paragraph). But if I’m the only person searching for this stuff, you better not hold your breath waiting for the next update, because it might be some time.
Hi Nick,
thanks for this post! I’ve been following research on the Voynich manuscript for over 20 years now (thanks to the YouTube algorithm for pulling me down this rabbit hole 😉).
I remember that when I first saw the scans of the manuscript pages, I thought to myself: These gallows characters look like some sort of instruction on how to read the text… But then again, how would that explain the unusually low word entropy observed in the manuscript?
Jürgen Plötner: explanations are easy to construct, easy to tweak when someone complains, and usually tell you next to nothing – most supposed “explanations” do nothing but explain away the problem (i.e. why they think the problem isn’t actually a problem), without actually solving it. The right questions to ask are more concrete, and are more along the lines of: what concrete mechanisms can account for these behaviours?
In the Voynich manuscript, one of the (multiple) concrete mechanisms I strongly believe is in play is verbose cipher (which I mentioned briefly in the article). This would be where multiple glyphs encipher a plaintext letter, e.g. qo / or / ol / ar / al all encipher a single plaintext letter. (I don’t include ch and sh here because they’re both single glyphs that the EVA transcription has turned into multiple letters.) This yields very predictable follow-on pairs, which has the effect of skewing the entropy statistics (which is what I believe you’re asking about).
Nick, the context you describe –
“.. that the cipher creator had shown the first evolutionary stage to multiple potential patrons, in an attempt to sell his cryptographic / intelligencer services to them: or else there would have been no need for tricky misdirection. So I believe this tells a story not of a complete outsider, but rather of someone on the periphery of one or more fifteenth century courts, trying to use their cryptographic smarts to gain patronage.”
would offer a possible resolution to the old paradox – ‘why encipher a well-known text?’ To seeing a block of ‘impossible’ text transformed before your eyes, as it was being deciphered, into something very well known – as e.g. a recipe for Pepper Water – would surely impress.
One niggle, though – if the aim were to present courtly fifteenth-century Latins with a guide to that cryptographic method, why include so many drawings, and drawings in a style so *very* unlike the style which, we know, appealed to the taste of contemporary nobles in Latin Europe? I’m not saying you need to have an answer for this – another ‘whereof’ probably – but it is another among the questions raised by this troublesome old ms.
The thread on the (close to) statistical independence between prefix before & suffix after EVA ‘k’ in Bio B words (https://www.voynich.ninja/thread-4764.html) is a new item high on my list of constraints on theories. I wonder how roughly statistically independent word final and word intial digrams or trigrams are in various natural languages…
Karl: that’s a strong-looking result. Maybe the proof I’m looking for will be found in combining line-initial tokens with k-prefix and k-suffix values on that line. Thanks!
Nick
Thank you for your 20 years of study .
I tio have spent 20 years publishing number theory aspects of the
of the officially unbroken 1925 BCe Akhmim Wooden Tablet. The five problems
divided one volume unit (hekat) by n =. 3. 7, 10, 11, 13, and five proofs built upon multiplication and division as fully inverse operations to one another .
Quotient (Q) and Remainder (R) were first encoded by changing a division problem into a multiplication problem , and proved each answer correct by multiplying each n answer by the initial divisor , returned 64/64 , the initial hekat scaling factor .
My unsolved problem actually is 160 years old , related to the first Western
efforts to decode Egyptian fraction math contained in the Berlin Papyrus ,
and the RMP. The RMP was placed in the British museum in 1863, related to the untimely death of Henry Rhind who purchased the RMP and EMLR on the streets of Cairo in 1858.
An formal paper paper explaining the following is available .
64/64 x 1/n = (Q/64 + 5R /n(1/320)
For 100 years scholars like Chace, et al, have claimed success in decioding the 87 problem Rhind Mathematical Papyrus , written by Ahmes in 1659 BCE..
Nick
I too have worked 20 years on an unsolved problem the proof side of the 1925 BCE Akhmim Wooden Tablet .
The initial quotient and remainder answers were published in 2006
https://www.academia.edu/74318674/The_Arithmetic_used_to_Solve_an_Ancient_Horus_Eye_Problem
connected to like problems left unsolved by Chace, et al, 1927 , such the
n = 6,, 20, 40 divisions of a hekat in RMP 81, Ahmes bird feeding problem .
The unsolved proof side has been solved , and will be published as an
appendix to a longer narrative connecting Egyptian fraction math from 2050 BCE Egypt to Greeks, Arabs , Fibonacci and Galileo in 1600 CE. a period of 3,650 years .
Best Regards
Milo Gardner , Cryptanalyst
Trained by US Army 1957
broke Russian and Arabic
codes 1957-1959
The Gallows is one of the simpler Problems to overcome. As they mostly occur on designated positions they must represent a second garniture of letters, represented by orher glyphs elsewhere. As always it’s futile to give these hints…
It is as certain that they are now ignored as it is certain that there will be no progress with the Voynich at all…
Sh, ch… These are one glyphs because Most probably they are one single letter in the plaintext – put away your Europeen glasses
I’ve been working on a hypothesis on folio 29v called the “Latinbrew Theory”: I believe the author was a native Hebrew speaker learning Latin, and the writer was encoding Latin plant or ritual knowledge phonetically via Hebrew logic and mapping the visual form of Latin letter shapes into Voynich glyphs.
I used AI to apply that logic, and what I’ve found is that 29v specifically reads exactly like a herbal procedure list.
I think the entire page reads:
Boil gourd twice with valerian, then add bark? (Unconfirmed on bark)
Boil gourd, cannabis, valerian;
repeat boil & cannabis
Chamomile, celandine, sage, cotula, basil
Chamomile x2, nigella seed x2, gourd
Cannabis x2, nigella seed, valerian, chamomile
Sage x2, basil, bark, nigella seed
Nigella seed, cannabis, chamomile, cannabis, valerian
@I dunno man
Sounds like the usual sort of medico-pharmaceutical recipe, Why add ‘ritual’?.
@ I dunno man,
perhaps for ‘gourd’ ‘curcubit’? Term for a vessel shaped like a bottle-gourd.
Nick, here there. Hope you are well. How closely do you hold this hypothesis? Is it
replacing your Antonio Averlino/ Filarete guess or just a new Alternative?
Not exactly a cipher, Nick, but you might enjoy a couple of articles by Michael Lapdige and Peter S. Baker which talk about work by Abbo of Fleury. I was interested in it when working on the Voynich map and looking into concepts of co-ordinates and position.
One of their articles, ‘More Acrostic Verse by Abbo of Fleury’ was published in 1997 in The Journal of Medieval Latin (Vol. 7 pp.1-27.)
Incidentally connects with use of Hyginus, which is nice because my first impression of some among the calendar’s month emblems was that they were akin to forms used in early Fleury.
PS – I’m sorry to say that after so long I can’t recall if I took my photocopy from the Journal, or printed it off from some online pdf.
What are your thoughts on the naibbe cipher?
Nick,
What are your thoughts on labels in the context of this method?
It is certainly interestingly to explore vertical and horizontal triggers to alternate alphabets that evolved in complexity over time; however, it would take a strange mind indeed to develop an entirely separate system for the standalone labels. Curious if you have thoughts on how the labels fit into this type of system.
Tim T: when I thought about labelese back when I was writing Curse, I wondered whether o + gallows (e.g. in ‘otolal’) and y + gallows (which also appears disproportionately often in labels, as I recall) might be a verbose cipher way of filling in the gaps left by the inapplicability of transposition cipher to non-block-structured text.
Thx Nick,
Understanding its quite impossible to have an original discussion on decades old topic, but just wanted to explore any new ideas on multi-alphabet triggers within a word (without being verbose) as that’s one of the few ways I imagine the labels, acting as labels.
Cheers,
Tim T.
Hi. This doesn’t relate to the matter at hand, but it crossed my mind. Does anyone know what Umberto Eco thought of the Voynich manuscript? He was obviously interested in it as if you get a copy of the Yale facsimile he has his picture taken for it, so it isn’t impossible that he spoke to someone at Yale about it. I don’t know his level of cryptographic skill, but he seems like a person that would have been a good person to put it in context given its guessed upon timeframe.
At the end of the article, Nick asks “Where to go next”. And you also look for some visual clue in the manuscript. The visual clue that the author Eliška shows to everyone who is trying to decipher the text is located at the very beginning of the manuscript. Specifically, on the page marked folio 2r. On that folio, a homophonic substitution cipher of the number 3 is shown. This is a very important clue. Every scientist should therefore first find out what substitution cipher it is. The cipher is generally called: Kabbalistic numerological system of gematria. At the root of that symbolic plant are the letters C, G, S, L. (that is a whole series of letters of the number 3). Without knowledge of that Jewish substitution, no one will ever be able to decipher the text of the manuscript. What is more important, in order for someone to be able to decipher the text, they must know the old Czech language, in which the text itself is written. The researcher should also be able to speak German, Polish and Latin. Because there are several of those words in the text of the manuscript. Next, what is important. It is important to know the letters that are in the handwriting. The EVA alphabet is good at about 30 percent. And because there is a very complex substitution cipher when writing handwriting, where one character can be replaced by 4 letters, frequency analysis is out of the question.