Following my first post on “Thomas Torrance Keane” (and my second post correcting his name to “Thomas Lawrence Keane”, thanks Debra! 🙂 ), I’ve been wondering which particular archival wall I should bang my head against next. At some point in the next few months, his WW2 records should now appear on the web… but as to what they will reveal, I have no idea at all.
In Keane’s funeral notices, there was one tiny dangling thread asking to be gently tugged at: his membership of the RSSAILA, the Returned Sailor’s, Soldier’s and Airmen’s Imperial League of Australia:-
KEANE.—New Farm Sub-branch, R.S.S.A.I.L.A. —The Officers and Members are invited to attend the Funeral of their late Member, Mr. T. L. Keane, to move from Alex. Gow’s Funeral Chapel, as per family notice. A. L Beeston, Secretary.
The RSSAILA was originally formed during WW1 as the RSSILA: with the addition of “A” (for “Airmen’s”) in 1940, it then became the RSSAILA, before eventually becoming the RSL (“Returned & Services League of Australia”) in 1965.
Descriptions of the RSSILA in its very early years that I’ve read online make it sound like a right-wing activist organization, with plenty of government and intelligence informers ensconced in key posts: but where the later RSSAILA found itself in the politically-divided post-WW2 years, I don’t know.
Anyway, I thought I’d see if any newsletters or documents pertaining to the RSSILA/RSSAILA’s New Farm Sub-branch still existed: so contacted the branch. “Unfortunately,” the answer speedily came back, “being situated on the Brisbane River, most of our records were lost in the 1974 floods that devastated Brisbane in that year.” Perhaps the South Eastern District did have a newsletter circa 1948-1949, perhaps it didn’t: nobody remembers any more, it all seems to be a bit of a haze.
Of course, there may yet be something relevant deep within the National Archives of Australia’s MS 6609 (which, as I noted before, contains “a rather scary-sounding 205 linear metres of RSL archives”, and may well not have any practical finding aid). But all the same, I think we ought to exhaust other avenues before searching for a spider in that particular dark hole. 🙂
Searching on the ever-surprising Trove did turn up something a little bit odd. In 1st February 1929, Mr. T. H. Keane was elected the assistant Hon. secretary of the South Eastern Queensland district branch: while on 21st July 1930, T. H. Keene was elected one of three vice-presidents of the District, as well as “delegate to the Federal executive”. By 20th July 1931, T. H. Keene was “acting president”, and again nominated for state vice-president: and on 1st September 1931 he appears (as “T. Keane”) in the list of delegates at the annual State conference.
Helpfully, the Brisbane Courier ran a short piece on him when he was voted in as president:-
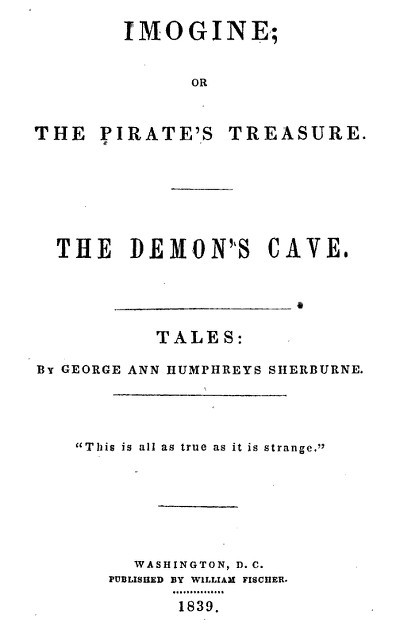
At the meeting of the South-eastern Queensland district Executive of the R.S.S.I.L.A., held at Anzac House on Friday night, the district president was elected. The two candidates were Major Taylor (former president, resigned) and Mr. T. H. Keene (vice chairman), and the ballot resulted in the success of Mr. Keene. The new district president (Mr. T. H. Keene) has a fine record. He returned from active service with the 49th Battalion overseas for approximately three years, during which he was wounded several times. In 1919 he joined the Ithaca sub-branch of the R.S.S.I.L.A., and was later transferred to the Toowong sub-branch, where he has remained since. For five years Mr. Keene represented the Toowong sub-branch on the South-eastern Queensland district executive, and whilst a member of the latter-named body he acted as assistant honorary district secretary, vice-chairman, and delegate to the State managerial council, and recently was elected as emergency delegate to the forthcoming State executive meeting.
And yes, there’s even a photo of him:-
It is here, however, that our all-too-fine historical thread finally snaps: this particular T. H. Keene was in the 49th Battalion, whereas the Thomas Lawrence Keane we’re interested in was “late 15th & 57th Bns., 1st A.I.F.” So, despite the many overlaps and misspellings, this T. H. Keene was apparently someone else entirely. Oh well, hopefully this will prevent anyone else from haring down this particular empty rabbit hole! 😐