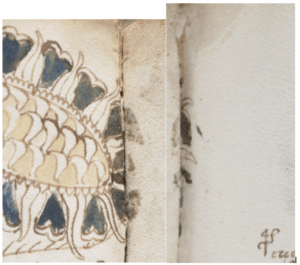
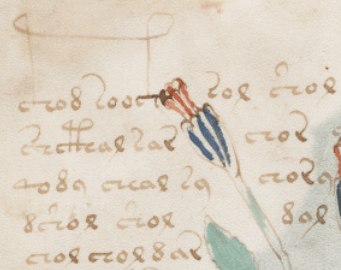
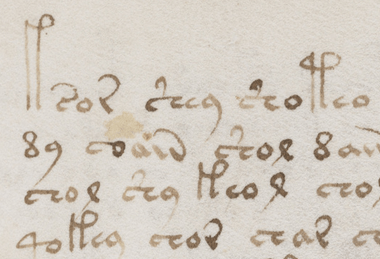
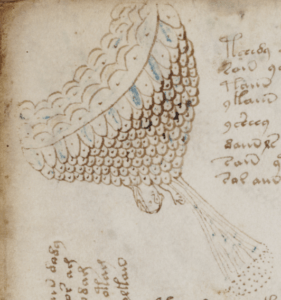
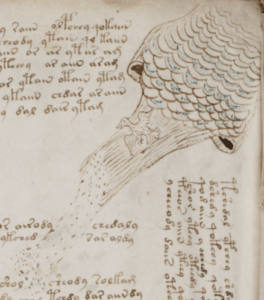
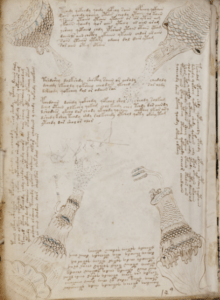
For some years, I’ve been wondering about Italian vernacular recipe collections similar to the one by Alcherio translated into Latin by Jehan le Begue in Paris in 1431. This is simply because I have a strong suspicion that the Voynich Manuscript’s Q20 (which is made up of starred paragraphs, each of broadly recipe-like size) contains a set of (you guessed it) Italian-language vernacular recipes. And if I can identify an Italian plaintext for a good selection of these recipes, I might be able to use that as a way to launch a “block paradigm” attack on Q20 (i.e. figure out a probable plaintext for even one of the paragraphs).
But… the problem here was always not about what I want to know, but about how to find it out. Even if you dive into the De Coloribus et Mixtionibus (“DCM”, a well-known family of Latin recipe mss) literature (e.g. Rozelle Johnson in the 1930s), the overwhelming majority of that relates to textual derivations between Latin recipes. (Johnson mentions briefly that an Italian-language copy of DCM recipe A1 appears in MS Ashburnhamiana 349, but never goes further than that.) Even Travaglio doesn’t really delve significantly into Italian vernacular translations of DCM recipes, essentially taking Johnson’s Latin-centric framework as a given only to be explored.
However, a few days ago I suddenly remembered that a few years back I had bought a copy of Mark Clarke’s (2001) “The Art of All Colours”: and when I (finally) read that properly, this whole unclear research landscape fell into sharp focus. Clarke lists more than 400 medieval manuscripts, giving proper shelfmark and language notes, plus references to textual editions and references where he is aware of them. (This is a biiiiig landscape for a single book to cover.) And so I now have a modest (but usable) set of 14th-15th century Italian language recipes to try to understand.
Italian-language recipe mss listed in Clarke (2001)
Here’s my work-in-progress list of pre-1500 Italian-language recipe mss extracted from Mark Clarke’s most excellent (2001) “The Art of All Colours”. The numbers (155, 160 etc) are Clarke’s numbering scheme.
- Lehigh University
- 155: Ms. 57 – in Latin, Catalan, and Italian (see Wilson 1936)
- Bologna, Biblioteca Universitaria
- 160: Ms. 1536, the “Bolognese Ms.”, 249 fols, in Latin and Italian (ED and TR in Merrifield 1849)
- Ferrara, Biblioteca Communale Ariostea
- 582: Ms. Cl. II 147 ff. 64r-194 (pseudo-Savonarola) in Italian and Latin. ED: Torresi 1992
- 585: Ms. 861 ff. 84r-95v, in Latin and Italian. ED: Torresi 1993b
- Florence, Biblioteca Medicea-Laurenziana
- 590: Ms. XXIII, plut 78. Cennino Cennini, “Il Libro dell’Arte” (For TR, see Thompson 1933a)
- 630: Ms. Ashburnhamiana 349. ff. 55f & 84r have ink recipes in Italian
- 655: “Ms. 2558” (in Brunello): dyeing recipes
- Florence, Biblioteca Nazionale Centrale
- 660: Ms Magliabacchi XV 8 b
- 700: “Magliabacchi 60” (?) (in Brunello): dyeing recipes
- 705: Ms. Palatina 567, (in Brunello): dyeing recipes
- 708: Ms. Palatina 718, recipes to dye wood, ED. Pomaro 1991
- 720: Ms. Palatina 763, in Italian and Latin, ED. Pomaro 1991
- 750: Ms. Palatina 796, ED. Pomaro 1991
- 755: Ms. Palatina 811, in Latin and Italian, ED. Pomaro 1991
- 770: Ms. Palatina 850, ED. Pomaro 1991
- 790: Ms. Palatina 857, ED. Pomaro 1991
- 800: Ms. Palatina 860, recipes from the Mappae Clavicula, in Italian and Latin, ED. Pomaro 1991
- 810: Ms. Palatina 862, ED. Pomaro 1991
- 820: Ms. Palatina 865, ED. Pomaro 1991
- 825: Ms. Palatina 885, in Italian and Latin, ED. Pomaro 1991
- 830: Ms. Palatina 886, in Italian and Latin, ED. Pomaro 1991
- 840: Ms. Palatina 916, (ff. 50r-162v), ED. Pomaro 1991
- 870: Ms. Palatina 934, ED. Pomaro 1991
- 875: Ms. Palatina 945, ED. Pomaro 1991
- 878: Ms. Palatina 949, ED. Pomaro 1991
- 900: Ms. Palatina 1001, ED. Pomaro 1991
- 905: Ms. Palatina 1021, ED. Pomaro 1991
- 912: Ms. Palatina 1026, ED. Pomaro 1991
- 920: Ms. Palatina 1072, in Italian and Latin, ED. Pomaro 1991
- 928: “Strozziano 181” (?), dyeing, in Brunello
- Florence, Biblioteca Ricciardiana
- 990: Ms. 1246, ff. 13r-92v
- 1000: Ms. 1247, ff. 9v-49r
- 1020: Ms. 2190 (late copy of Cennino Cennini)
- 1032: Ms. 2142, dyeing, in Brunello
- 1034: Ms. 2558, dyeing, in Brunello
- 1036: Ms. 2580, dyeing, in Brunello
- British Library
- 1770: Ms. Sloane 416 “The Venetian Manuscript”, in Netherlandish, Italian, and Latin (ED Italian in Tosatti 1991)
- London, Victoria & Albert Museum
- 2007: Ms. A.L. 1496/1893, ff. 13-16v, in Italian (said to be Venetian dialect)
- Lucca, Biblioteca Statale
- 2055: Ms. Cod. 1286, ED: Arrighi 1967
- Oxford, Bodleian Library
- 2460: Ms. Canonici Ital. 183
- Paris, Bibliotheque Nationale
- 2945: “Paris BN No. 916” (??), dyeing, in Brunello
- Rome, Biblioteca Casanatense
- 3040: Ms. 1477 (no language specified)
- 3050: Ms. 1793, ff. 10v-13v and 15v-20v
- Siena, Biblioteca Communale degli Intronati
- 3110: Ms. I.II.19, ff. 99r-106r, Ricepte d’Affare piu Colori, by Ambrogio di ser Pietro da Siena, 1462 (ED: Thompson 1933b and Torresi 1993b)
- 3120: Ms. L.XI.41, ff. 34v-41, ED: Tosatti-Soldano 1978 pp. 139-149
- Vatican, Biblioteca Apostolica Vaticana
- 3300: Ms. Vat. lat. 6852, Praecepta Colorum of Felice Feliciano, in “Italianate Latin”, 1433-1479
- “Location Uncertain”
- 3580: “a treatise in Italian on several art techniques…”, ED Malaguzzi Valeri (1896)
As I’m sure you’d guess, this is the point in my research where I typically start to fill up a bookshelf with obscure monographs. Oddly, here, most appear to be tightly clustered around 1991-1993 (so it’s clearly what all the cool kids were researching back then):
- For most of the recipes in the Biblioteca Nazionale Centrale, see:
- Pomaro, G. (1991) “I Recettari del Fondo della Biblioteca nazionale centrale di Firenze. Inventari e cataloghi toscani: 35″
- For the Italian parts of the Venetian Manuscript, see:
- Tosatti Soldano, B. S. (1991) “Il Manoscritto Veneziano“
- For Pseudo-Savonarola (later, but I believe the book looks backwards to Alcherio etc)
- Torresi, A. P. (1992) “A far littere de oro“
- For Ferrara Ms. 861 ff., see:
- Torresi, A. P. (1993) “Il taccuino Antonelli : un ricettario ferrarese del Quattrocento di tecnica artistica e fitoterapia“
Unfortunately, these are all obscure/rare enough to make Bookfinder weep. Sure, I was able to order Tosatti Soldano’s “Il Manoscritto Veneziano” from FirenzeLibri, but as for the rest? Fat chance.
So, the good news is that there is a pre-existing literature for me to grind my way through. The bad news is that it seems I can’t buy my way into it at any price. *sigh*